Incoming Record Audit – Espernofilia, Odoromalasaurus, 8664739239, 886279325026, 8002595924
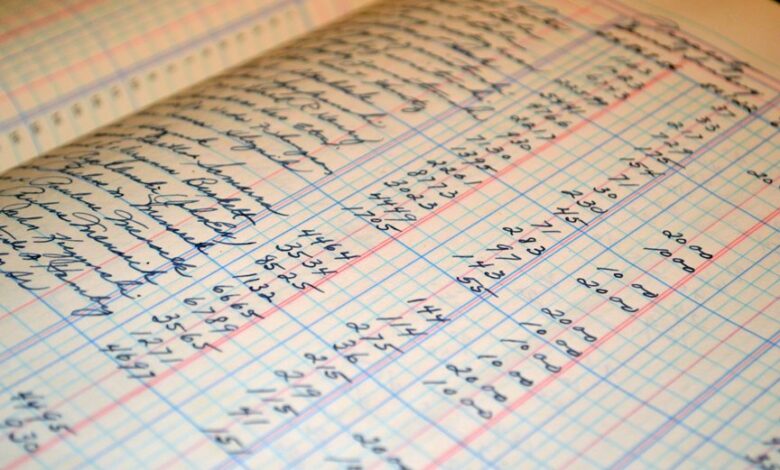
The incoming record audit for Espernofilia and Odoromalasaurus centers on formal verification against an audit trail. It examines provenance, validity, and access controls through cross-referenced identifiers 8664739239, 886279325026, and 8002595924. The process tracks origin, transformations, and permissions, using checksums and timestamps to confirm integrity. It addresses schema drift between legacy and modern standards, highlighting governance and repeatable validation. The outcome prompts a critical question that invites careful consideration and further analysis.
What Is the Incoming Record Audit for Espernofilia and Odoromalasaurus?
The incoming record audit for Espernofilia and Odoromalasaurus is a formal process designed to verify the completeness, accuracy, and integrity of newly received data. It evaluates the incoming record against an audit trail, tests provenance validity, enforces access controls, reconciles legacy entries, and aligns with modern standards to ensure reliability, transparency, and freedom in data governance.
How Do the Identifiers 8664739239, 886279325026, and 8002595924 Relate?
How do the identifiers 8664739239, 886279325026, and 8002595924 relate within the incoming record audit framework? They reflect distinct yet interconnected identifiers that anchor the same entity across stages, enabling cross-reference. This IDs interplay supports consistent dataset mapping, clarifying linkage between records and ensuring traceable alignment while preserving flexibility for evolving schemas and independent data origins.
Provenance, Validity, and Access Controls: Tracing the Audit Trail
Provenance, validity, and access controls together establish a transparent audit trail that tracks data origin, transformation, and permissioned use.
The analysis distinguishes lineage, confirms integrity through checksums and timestamps, and enforces policy via access controls.
Identified provenance gaps reveal where metadata or custody proofs are missing, guiding remediation.
Robust controls enable accountable, auditable, and freedom-supporting data stewardship.
Reconciliation Across Legacy and Modern Standards: Challenges and Solutions
Reconciliation between legacy and modern data standards presents a suite of cross-cutting challenges, including schema drift, divergent validation rules, and inconsistent metadata granularity. Analysts identify reconciliation gaps and pursue standards alignment through mapping, normalization, and governance. Limitations arise from heterogeneous tooling and institutional inertia; effective solutions require disciplined governance, transparent provenance, and measurable, repeatable validation across domains.
Frequently Asked Questions
How Is Data Privacy Maintained During the Audit Process?
Data privacy is maintained through data minimization and strict access controls; the audit limits collection to necessary information and enforces least-privilege access, with regular reviews, encryption, and audit trails to ensure accountability and protect individual confidentiality.
What Are the Audit’s Key Performance Indicators?
The audit’s key performance indicators emphasize audit governance effectiveness and data lineage accuracy, measuring timeliness, defect rates, and remediation velocity; results inform risk posture and continuous improvement, while preserving data autonomy and a transparent, freedom-respecting analytical framework.
Who Has Authorization to View Audit Results?
Access to audit results is restricted to authorized roles through strict access control, with least-privilege assignments. Data minimization principles guide disclosures, ensuring only necessary information is shared; permissions are auditable, reviewed periodically, and enforced consistently across custodians.
How Are Discrepancies Prioritized for Remediation?
Discrepancies are ranked by discrepancy severity, guiding remediation timing. The process is methodical, transparent, and governed by defined thresholds; prioritization balances risk, impact, and effort, enabling purposeful remediation while preserving freedom to adapt.
Can Audits Influence Future Data Ingestion Workflows?
Audits can influence future data ingestion workflows, as data governance and data lineage insights prompt adjustments to validation rules, metadata capture, and governance controls; this fosters proactive quality, traceability, and freedom to evolve ingestion practices.
Conclusion
The incoming record audit, meticulously measured, maps meticulous movements from origin to alteration, ensuring integrity and insight. Provenance paths, permissions, and persistent checksums form a coherent chronology, while cross-referenced anchors anchor alignment across schemas. Thorough thresholding of legacy gaps and modern metadata minimizes drift, delivering transparent traceability. Governance and repeatable validation underpin accountable stewardship. Precise provenance practices, persistent provenance procedures, and prudent permission protocols permeate the process, presenting a principled, procedural, Pythian-level panorama of prudent, persistent auditing.




