Account Data Review – 8285431493, mez68436136, 9173980781, 7804091305, 111.90.150.204l
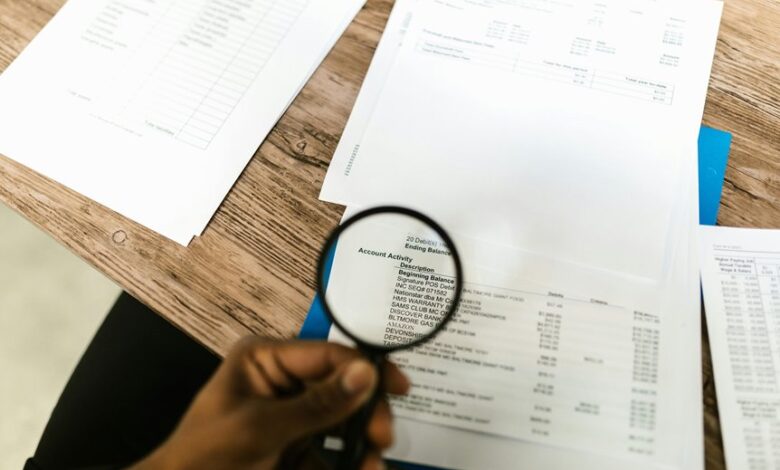
This account data review examines identifiers 8285431493, mez68436136, 9173980781, 7804091305, and the IP context 111.90.150.204l with a focus on discovery, profiling, and provenance tracing. It outlines data sources, ownership, and transformation steps, plus validation and governance roles. Metrics target completeness, accuracy, timeliness, and lineage. Cross-domain linkages and IP patterns are monitored for anomalies. The process enforces access controls and remains auditable, supporting ongoing integrity and security hygiene while signaling what comes next.
What an Account Data Review Covers for 8285431493 and Friends
Account data reviews for 8285431493 and its related entities systematically identify scope, criteria, and frequency.
The process emphasizes account discovery and data profiling to delineate data sources, ownership, and transformation steps.
Metrics include completeness, accuracy, timeliness, and lineage.
Documentation enumerates roles, access controls, and validation checks, ensuring transparent governance while preserving autonomy and freedom through precise, numbers-driven evaluation.
Spotting Red Flags in Linked Data and IP Contexts
Linked data and IP context analysis builds on the structured scope and metrics established in the prior account data review, extending the evaluation to interconnections, ownership chains, and access patterns.
Systematic monitoring identifies anomalies: inconsistent ownership, abrupt access spikes, cross-domain linking, and suspicious geo-IP shifts.
Spotting redflags in ip contexts enables rapid triage, documenting variance, and sustaining defensible data integrity.
Step-by-Step Checklist to Strengthen Data Integrity
A step-by-step checklist for strengthening data integrity enumerates concrete actions to verify accuracy, consistency, and provenance across datasets.
The procedure enumerates measurable controls: data integrity, validation rules, versioning, and provenance trails.
Security hygiene is integrated, including access audits and anomaly detection.
Data governance assigns responsibilities, while risk mitigation protocols prioritize critical data assets and periodic reviews for continuous improvement.
Practical Next Steps for Ongoing Data Hygiene and Security
To maintain ongoing data hygiene and security, organizations should implement a structured cadence of practical steps: establish continuous data quality monitoring, enforce strict access controls, and align governance with real-time risk assessment.
Practitioners quantify risk, map data flows, implement baseline security basics, audit permissions, automate anomaly detection, and document metrics.
This disciplined approach preserves data hygiene and sustains security basics with measurable outcomes.
Frequently Asked Questions
How Is Personal Data Ownership Determined Across Linked Accounts?
Ownership is determined through ownership mapping across linked accounts, establishing primary data custodians and rights. Consent provenance is traced to originators, with policy-driven resolution guiding transfers, mergers, and deletions; decisions reflect freedom-minded compliance and auditable accountability.
Can Data Reviews Reveal Past Data Breaches Affecting These Numbers?
Data breach history can be revealed by reviews, though linked accounts ownership complicates attribution. Juxtaposition frames risk versus control; data breach history informs accountability while maintaining privacy. Reviews quantify incidents, timelines, scope, and impact across connected profiles.
What Tools Verify the Authenticity of External Data Sources?
Tools verifying authenticity of external data sources include cryptographic signatures, checksums, and provenance tracking systems; assess source credibility, data provenance, integrity, audit trails, and tamper-evidence to ensure trustworthy, independent verification for data-driven decisions.
Are There Industry-Specific Compliance Gaps to Address?
Yes, there are industry-specific compliance gaps to address. Specific gaps vary by sector, but common areas include data retention, cross-border transfers, access controls, auditability, and alignment with evolving industry standards and regulator guidance.
How Frequently Should Audit Logs Be Archived and Purged?
Logs should be archived and purged on a defined schedule. The cadence: monthly archiving, quarterly purge, with retention tied to data lifecycle management. Scheduling retention requires precise timestamps, policy thresholds, and automated workflows for consistent, auditable results.
Conclusion
The account data review demonstrates a precise, methodical approach to data provenance, transformation, and governance. By enumerating sources, ownership, and validation rules, the process yields measurable metrics for completeness, accuracy, and timeliness. An anticipated objection—claims of bureaucratic overhead—is negated by a stepwise, auditable workflow that enables rapid anomaly detection and remediation. Overall, the framework supports continuous improvement, cross-domain linkage monitoring, and reinforced access controls, sustaining ongoing data hygiene and security posture.




